AlexCTF 2017 - SC2 Cutie Cat
Category: writeupsTags: alexctf-2017 scripting stego
SC2: Cutie Cat
Scripting - 150 Points
yeah steganography challenges are the worst… that’s why we got only ~~one ~~ two steganography challenges .
Writeup

We are given a valid PNG image of a kitten. A classic for CTF competitions. Using the reverse image search function on google, we find an almost identical image in height/width/size. Using compare cat_with_secrets.png original.png -compose src diff.png we extract the differences:
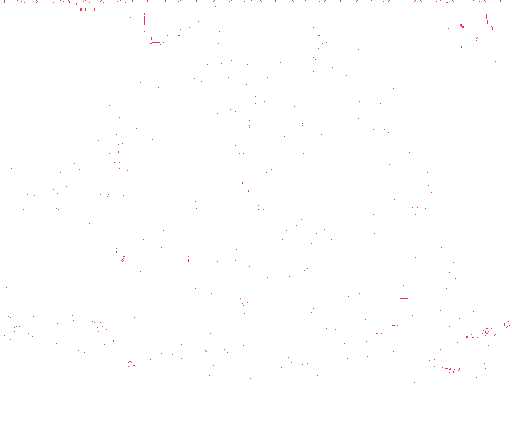
We observe that in the first 3 rows of pixels, they seems to differ at somewhat regular intervals:

If we print out the x values of these pixels, we get:
4 17 36 60 68 85 101 120 132 147 165 180 196 214 231 251 260 275 292 305 325 340 357 371 389 415 420 440 452 473 484 500 4 21 37 63 69 83 100 117 132 147 165 178 196 213 229 244 261 275 293 319 324 340 356 383 388 414 421 436 453 479 485 500 4 24 36 53 69 89 103 125
When converted to hex:
04 11 24 3c 44 55 65 78 84 93 a5 b4 c4 d6 e7 fb 104 113 124 131 145 154 165 173 185 19f 1a4 1b8 1c4 1d9 1e4 1f4 04 15 25 3f 45 53 64 75 84 93 a5 b2 c4 d5 e5 f4 105 113 125 13f 144 154 164 17f 184 19e 1a5 1b4 1c5 1df 1e5 1f4 04 18 24 35 45 59 67 7d
The first hex character increments by 1 for each extracted pixel. What if we just take the lower nibble in each hex value?
414c45584354467b434154535f484944455f534543524554535f444f4e545f544845597d
which decodes to ALEXCTF{CATS_HIDE_SECRETS_DONT_THEY}.
The full script for the extraction is available.